Calling an external payment provider sounds simple — until reliability, latency, secrets, failover, and rate limits start breaking production.
This is where many systems quietly become fragile.
The application code begins innocent enough: call the provider, wait for a response, handle success or failure. But over time, the business logic gets polluted with retries, timeout handling, fallback rules, authentication headers, region selection, and defensive logic for every third-party dependency. What started as a clean service slowly turns into a survival mechanism for unreliable networks.
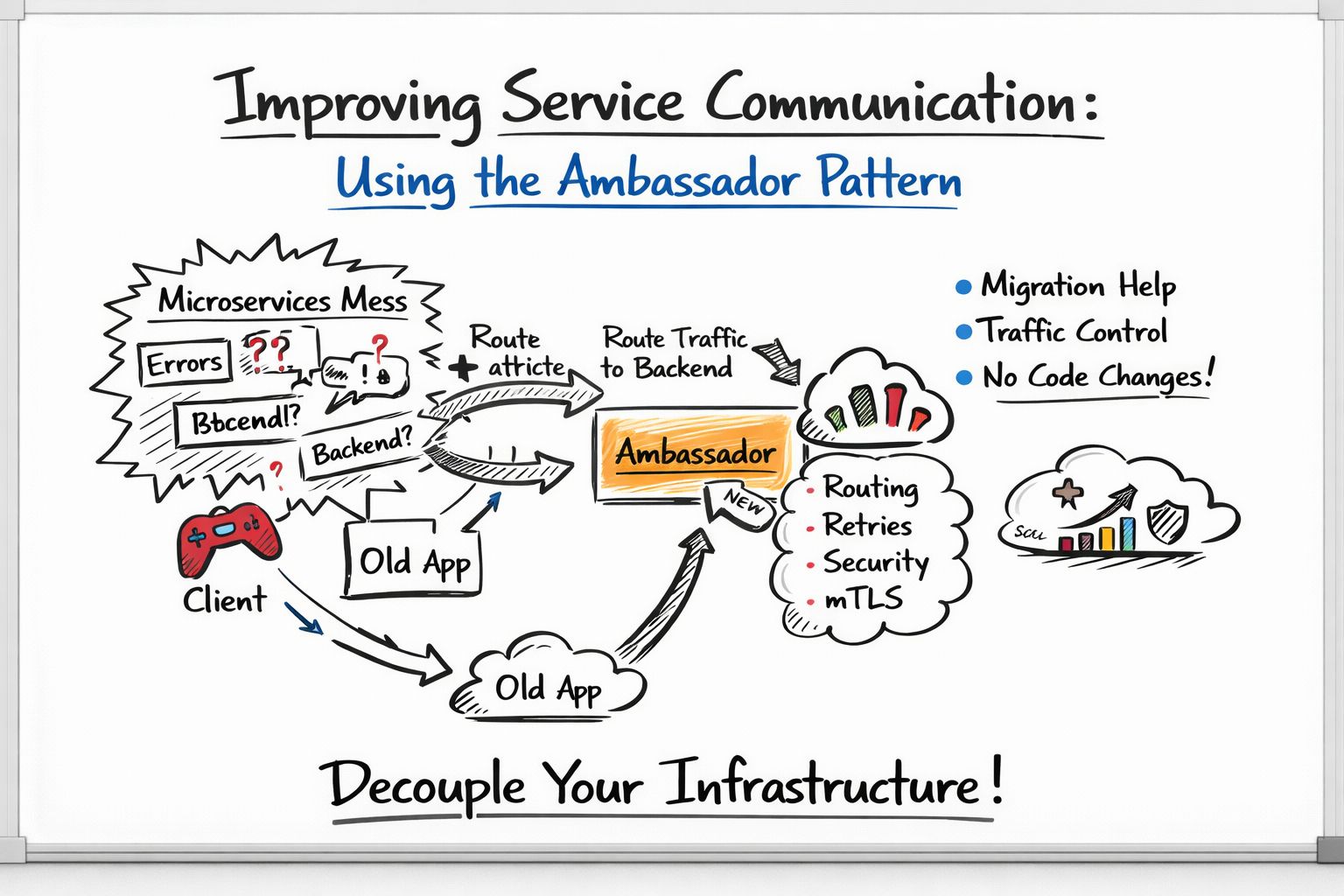
A better pattern is to stop letting the application talk to external providers directly.
Instead, introduce an Ambassador layer between your service and the third-party API.
That ambassador becomes the dedicated outbound gateway for external communication. It owns resilience. It owns routing. It owns security. It owns observability. And your application stays focused on business logic.
For something like external payment reliability, the ambassador can enforce timeouts, retries, and circuit breakers so transient failures do not immediately cascade into your core service. Rather than every developer implementing outbound protections differently, the logic becomes centralized and consistent. If you want to go one step further, Envoy Proxy is a strong fit here because it gives production-grade resilience features without forcing the application to carry that burden itself.
Now consider multi-region API routing. Suppose the provider exposes separate US and EU endpoints. Hardcoding endpoint logic in the application quickly becomes messy. The ambassador can dynamically choose the correct region, apply failover when one endpoint becomes unhealthy, and even evolve into latency-aware routing over time. This keeps regional routing decisions outside the business code and makes operational changes far easier.
Security improves as well. One of the most common mistakes in external integrations is exposing API keys too close to the application. A cleaner pattern is to keep credentials in AWS Secrets Manager, let the ambassador retrieve or inject them securely, and ensure the application itself never directly handles the raw secrets. This sharply reduces leakage risk and simplifies secret rotation.
Then comes rate limiting, which is especially important when a third-party provider has strict quotas. The ambassador can throttle outbound calls before they become a problem, and where needed, requests can be queued instead of immediately dropped. That turns a provider’s hard limit into a managed operational concern rather than an unpredictable application failure.
Observability becomes much stronger too. Since every outbound request passes through the ambassador, it becomes the natural place to capture latency, failure rates, response codes, and retry behavior. From there, metrics and logs can flow into Prometheus, CloudWatch, or any standard monitoring stack. Instead of guessing whether an issue is inside your service or outside it, you get a much clearer operational picture.
This pattern is also incredibly useful during monolith migration. Legacy systems often call external APIs directly from deeply embedded code paths. Rewriting all of that at once is risky. Introducing an ambassador allows you to gradually redirect outbound traffic through a controlled layer without forcing a major rewrite. Over time, the monolith becomes less tightly coupled to third-party integrations, and the migration becomes much safer.
The deeper lesson is simple: external APIs should not be treated like local method calls.
They are unstable boundaries.
They fail differently.
They need protection.
And the cleanest systems are often the ones that isolate that complexity behind a dedicated outbound layer.
If you are designing modern distributed systems, the Ambassador pattern is not just a networking trick — it is a strategic way to protect application code from the chaos of the outside world.
Subscribe for more.
