When teams adopt microservices, they think they are simplifying systems.
But something subtle happens.
Each service starts carrying responsibilities it was never meant to handle:
Authentication
Authorization
Secrets handling
Retries and resilience
Service discovery
None of this is business logic.
Yet, it slowly becomes the majority of your code.
And worse—every team implements it differently.
This is where systems start drifting toward inconsistency, security risks, and operational complexity.
The Shift: Moving Concerns Out of Code
At some point, a realization hits: Why is every service responsible for security? Why is authorization duplicated everywhere? Why are secrets even visible to developers?
The answer is not better code. The answer is better architecture.Instead of embedding these concerns inside services, we move them into managed infrastructure layers.
Quietly. Consistently. Systematically.
The Architecture That Changes the Game
This is where a new pattern emerges.
A combination of four AWS services that, together, reshape how microservices operate:
Amazon ECS → Runs your services
AWS VPC Lattice → Handles service-to-service communication
AWS Verified Permissions → Centralized policy engine (PDP)
AWS Secrets Manager → Secure runtime credentials
Individually, they are powerful.
Together, they form a system where:
Security is centralized
Networking is simplified
Authorization is consistent
Secrets are never exposed

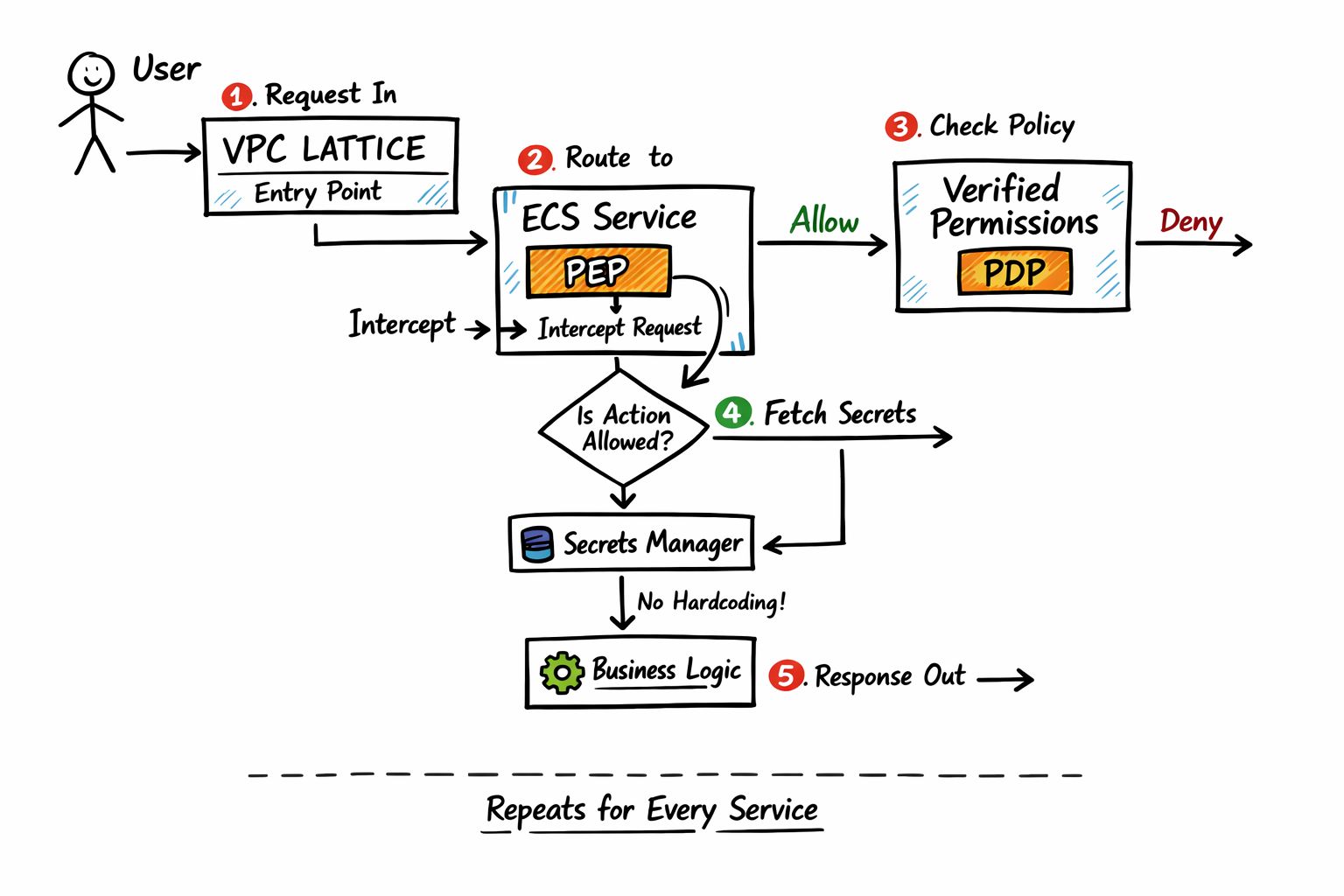
How the Flow Actually Works
Let’s walk through a real request: A user hits your system.The request enters through a single entry point powered by VPC Lattice.It is routed to a service running on ECS.
Inside the service, a lightweight PEP (Policy Enforcement Point) intercepts the request.
Before doing anything, it asks:
“Is this action allowed?”
That request goes to Verified Permissions.
A decision comes back: Allow or Deny.
If allowed, the service retrieves secrets dynamically from Secrets Manager.
No hardcoding. No environment leaks.
The service executes the business logic and returns the response.
This pattern repeats across every service.
Consistently.
Why This Is a Big Deal
This architecture removes entire categories of problems:
No duplicated authorization logic
No secrets embedded in configs
No service mesh operational overhead
No inconsistent security implementations
Instead, you get:
Centralized policy control
Fine-grained authorization
Secure secret access with rotation
Clean separation of concerns
This is not just cleaner.
It is safer, faster, and easier to scale.
The Subtle Power Most People Miss
The biggest advantage is not technical.
It’s organizational.
Now:
Security teams define policies
Platform teams manage infrastructure
Application teams focus only on business logic
This separation is what allows systems to scale without chaos.
Subscribe for more.
