Most microservices architectures encrypt traffic from the user to the load balancer…
But what happens after that?
Do you:
🔐 Terminate SSL at the Load Balancer?
or
🔐 Terminate SSL inside the container itself?
This single decision quietly affects:
• Security posture of your microservices
• Compliance readiness (HIPAA / PCI)
• Operational complexity
• Performance and debugging
Most teams choose the easy architecture.
But in regulated or high-security environments, that choice might not be enough.
In my latest Microservices Fundamentals breakdown, I explain:
✔ When SSL termination at ALB is perfectly acceptable
✔ When you must terminate SSL inside ECS tasks
✔ Why NGINX/Envoy sidecars are often recommended
✔ The hidden certificate management challenge inside containers
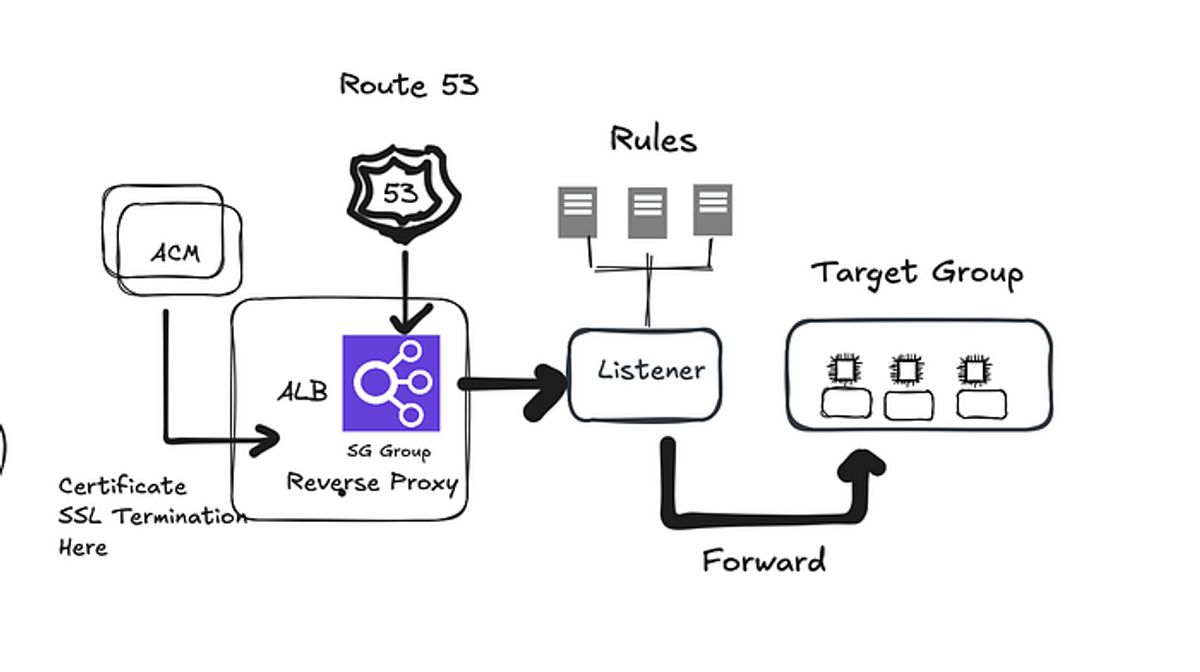
I also included two architecture diagrams to make the concept instantly clear.
If you are building Spring Boot microservices on AWS (ECS / Fargate), this design choice matters more than most people realize.